-
509.593.4207
- sales@viviotech.net
Looking for a promo code? Mention BOGOVPS2026 on any new VPS order and get your second month FREE!
Sophos UTM and Firewall
What's a UTM
Learn what a UTM is and how it can help you stay secure
Web Filtering
Protect your servers from incoming threats
Advanced Firewall
Adaptive threat protection from bad actors
VPN Features
Protect your servers in a "walled garden" network.
Clustering
Packet control for a variety of load balancing scenarios
What is a UTM?
A Full-Featured Security Appliance
- Unified Threat Management (UTM)
A Sophos UTM appliance is an appliance that brings together many different security solutions (like Firewall, VPN, Network Isolation, Web Filtering, etc) into a single location that make it easy to implement and manage. - Managed By Default
As a respected client of Vivio, your UTM will include Vivio’s expert SysOps Support by default. This means if you ever have a problem, a question, or simply need to bounce an idea of someone with experience, we’re always here to help. - Your Own “Walled Garden” Network
When you implement a Sophos UTM, by default you isolate your network and the services inside it from the outside world. Your UTM is designed to be the gateway to your network and services, and you have complete control over everything that goes in or out. It’s your own safe, private paradise.
Web Content Filtering
Protect your servers from incoming threats
Web-based threats occur in two main ways: 1) you either visit an infected website or open an infected email (outbound requests), or 2) your website or service is attacked directly using exploits such as SQL-Injection or Cross-Site Scripting (incoming requests). Your Sophos UTM can be configured to protect you and your users from both outbound and inbound attacks.
- Web Protection
The Sophos UTM Web Protection feature can be thought of as anti-virus for web sites that you are browsing. By analyzing the content that you’re visiting while browsing, your Sophos UTM can detect and block malicious content before it ever reaches any of your servers.
- Web Server Protection
Your Sophos UTM comes fully equipped with advanced incoming request filtering, often called a “Web Application Firewall” or a “WAF”, which will filter incoming requests for malicious content. SQLi, XSS, and other incoming attacks are blocked by this feature. Furthermore, if you have a sensitive login-screen that is frequently attacked – a WordPress admin login, for example – you can offload your authentication system to your UTM for an additional layer of enterprise-grade security.
Advanced Firewall
Full-Featured Firewall & Advanced Threat Protection
- Complete Application Control
Using the advanced, next-generation firewall available in your UTM, you can track and monitor all activity within your private network. Firewall rules can then be created either on a global scale, or a per-host scale, so that only specific applications have access to specific hosts. - Real-Time Application Network Throttling
As you monitor your network activity on your UTM, you can dynamically create rules on the fly based on what you’re seeing. If you see an unwanted application dominating your network, and you want to limit it’s activity, you can immediately create a rule to limit or block that specific application. - Advanced Threat Protection (ATP)
Using cloud-based heuristics and real-time diagnostics, your UTM has the ability to defend against threats that are as-yet unknown to the majority of the world. - Identify Compromised Hosts
Should the unthinkable happen and one of your servers does become a problem, the real-time reporting of Advanced Threat Protection will identify damaged hosts, as well as help determine specifics of how that host is a problem.
UTM VPN Features
Add another layer of protection with a VPN
A Virtual Private Network connection (VPN) allows you to connect directly to your Private Network here at Vivio. Once connected to your network, you can access your web servers, email servers, database servers, or anything else that you need access to that’s safely tucked away behind your Sophos UTM, as if your Vivio private network were right there with you. This gives you all the features and convenience of a robust hosted environment, along with all the freedom of a local network.
- VPN Client Options
Your Sophos UTM Supports a wide variety of VPN Connection options including the standard VPN Clients that come with Windows, Mac, or Linux Desktops; an installable, single-click desktop application; or even a web-based HTML5 enhanced VPN client that’s usable from just about any device. You’ll never have to worry about gaining secure access to your servers no matter where you are in the world or what devices you have available to you. - User Account Controls
As the administrator for your Sophos UTM, you have compete control over who accesses your private network, how they access it, and what specific machines each user has access to once their in your private network. You’re always in control, and with Vivio SysOps Support, you’re never alone if you ever have any questions. We’re here to serve.
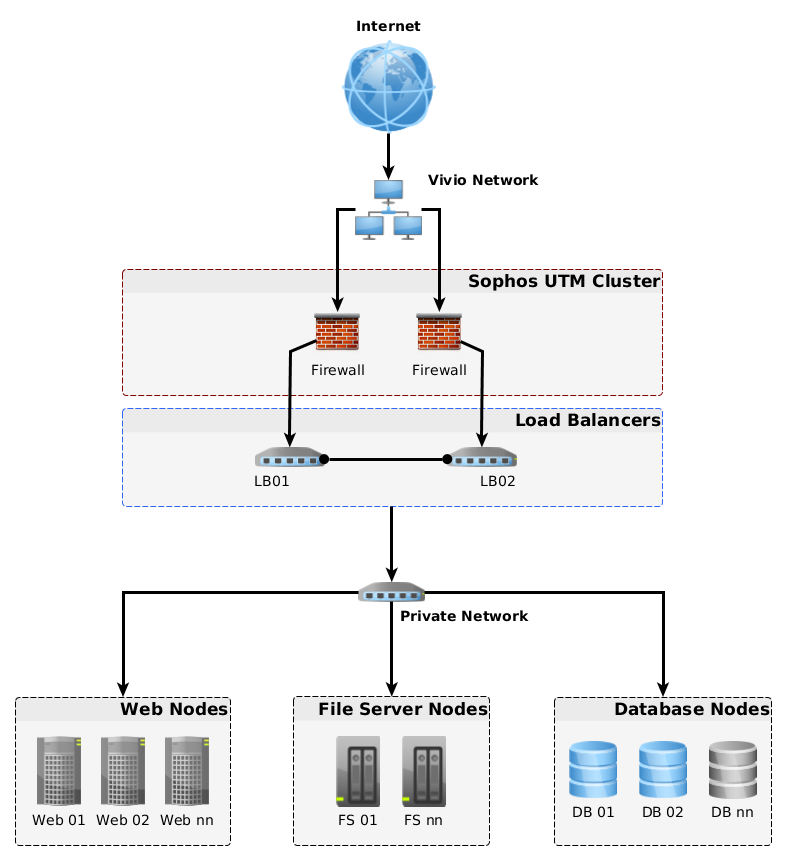
Flexible Clustering Options
Implement a UTM into any new or existing topology
Your Sophos UTM can be implemented in a huge variety of ways. Utilizing virtual switching, VLAN’s, and physical hardware (all handled by Vivio Support so you never have to worry about it), you can implement your UTM into any new or existing topology.
UTM’s themselves can also be clustered, eliminating any UTM as a single point of failure. With the Sophos UTM’s Intelligent Clustering capabilities, UTM’s can easily be configured in master/master mode, sharing workload and scaling up to huge numbers of UTM’s. This means that you have options that can support incredible throughput for a secure, clustered environment that can scale with you as you grow.

30-Day Money-Back Guarantee
Never settle. If you're unhappy with your Vivio account for any reason, simply cancel your account within 30 days for a full refund. No pressure. No risk. *Terms and Conditions may apply.

Backup Your Data Fast
Velocity Backups are powered by business-class SSD storage arrays - enabling you to backup, restore and manage your cloud backups faster than ever before.

Far far away, behind the word moun tains, far from the countries Vokalia and Consonantia, there live the blind texts. Separated they live in Bookmarksgrove right at the coast of
-
1473 Rose St
Walla Walla, WA 99362 -
sales@viviotech.net
Contact Sales -
support@viviotech.net
Contact Support
Switch The Language